Apush Chapter 28 Review Questions Identification the Baruch Plan
ane. When should a network performance baseline be measured?
- later normal piece of work hours to reduce possible interruptions
- during normal work hours of an organization*
- when a denial of service assault to the network is detected and blocked
- immediately after the main network devices restarted
2. What is a purpose of establishing a network baseline?
- Information technology provides a statistical average for network performance.
- It creates a betoken of reference for future network evaluations.*
- It manages the performance of network devices.
- It checks the security configuration of network devices.
3. Which three pieces of information are typically recorded in a logical topology diagram? (Cull three.)
- device models and manufacturers
- device locations
- cable specifications
- static routes*
- routing protocols*
- IP address and prefix lengths*
iv. In which step of gathering symptoms does the network engineer make up one's mind if the trouble is at the core, distribution, or admission layer of the network?
- Determine the symptoms.
- Narrow the scope.*
- Make up one's mind buying.
- Gather data.
- Document the symptoms.
5. A team of engineers has identified a solution to a significant network problem. The proposed solution is likely to affect critical network infrastructure components. What should the squad follow while implementing the solution to avoid interfering with other processes and infrastructure?
- syslog messages and reports
- one of the layered troubleshooting approaches
- knowledge base guidelines
- change-control procedures*
6. Refer to the exhibit. What action occurs at phase three of the general troubleshooting procedure?
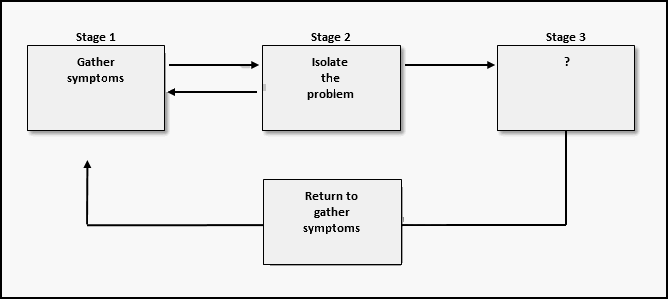
- Certificate symptoms.
- Question stop users.
- Narrow the scope.
- Correct the problem.*
7. After which step in the network troubleshooting process would i of the layered troubleshooting methods be used?
- documenting symptoms
- determining buying
- narrowing the scope
- gathering symptoms from suspect devices*
8. A network technician is troubleshooting an email connectedness problem. Which question to the stop-user volition provide clear information to improve define the problem?
- How big are the emails you tried to ship?
- What kind of equipment are yous using to send emails?
- Is your electronic mail working now?
- When did y'all starting time notice your email trouble?*
9. A network engineer is troubleshooting a network trouble and can successfully ping between ii devices. Withal, Telnet between the aforementioned two devices does not work. Which OSI layers should the administrator investigate next?
- from the network layer to the physical layer
- all of the layers
- but the network layer
- from the network layer to the awarding layer*
10. A network administrator is having issues with a newly installed network not appearing in other routers. At which layer of the OSI model is the network administrator going to starting time the troubleshooting procedure when using a top-downwardly arroyo?
- cyberspace
- application
- network*
- session
- transport
xi. Which troubleshooting method begins by examining cable connections and wiring issues?
- top-down
- separate-and-conquer
- substitution
- lesser-upwards*
12. Refer to the showroom. On the basis of the information presented, which two IP SLA related statements are true? (Choose ii.)
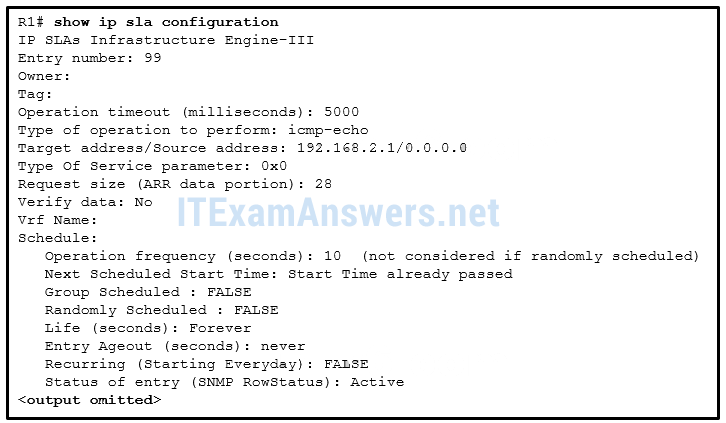
- IP SLA 99 will run forever unless explicitly disabled.*
- IP SLA 99 is measuring jitter.
- IP SLA 99 is configured with the blazon dns target-addr 192.168.2.1 command.
- IP SLA 99 is sending echo requests from IP accost 192.168.two.ane.
- IP SLA 99 is scheduled to begin in 2 hours.
- IP SLA 99 is sending echo requests every 10 seconds.*
13. A company is setting up a web site with SSL technology to protect the hallmark credentials required to access the web site. A network engineer needs to verify that the setup is correct and that the authentication is indeed encrypted. Which tool should be used?
- baselining tool
- cable analyzer
- protocol analyzer*
- fault-management tool
14. Which category of software troubleshooting tools provides device-level monitoring, configuration, and fault-management?
- host-based protocol analyzers
- baselining tools
- noesis bases
- network management system tools*
xv. Which two specialized troubleshooting tools can monitor the amount of traffic that passes through a switch? (Choose two.)
- DTX cablevision analyzer
- TDR
- digital multimeter
- portable network analyzer*
- NAM*
xvi. Which number represents the most severe level of syslog logging?
- 0*
- 1
- 6
- seven
17. A user in a large office calls technical back up to complain that a PC has suddenly lost connectivity to the network. The technician asks the caller to talk to nearby users to see if other machines are affected. The caller reports that several immediate neighbors in the same department have a similar problem and that they cannot ping each other. Those who are seated in other departments accept connectivity. What should the technician check as the first step in troubleshooting the issue?
- the power outlet to the PC that is used by the caller
- the cable connectedness between a PC and a network outlet that is used by a neighbor
- the cable that connects the PC of the caller to the network jack
- the status of the departmental workgroup switch in the wiring cupboard*
- the trunks between switches in the wiring closet
eighteen. A user reports that after an Os patch of the networking subsystem has been applied to a workstation, it performs very slowly when connecting to network resources. A network technician tests the link with a cable analyzer and notices that the workstation sends an excessive number of frames smaller than 64 bytes and also other meaningless frames. What is the possible cause of the problem?
- corrupted awarding installation
- cabling faults
- corrupted NIC commuter*
- Ethernet point attenuation
nineteen. An administrator is troubleshooting an Internet connectivity problem on a router. The output of the prove interfaces gigabitethernet 0/0 command reveals higher than normal framing errors on the interface that connects to the Cyberspace. At what layer of the OSI model is the problem likely occurring?
- Layer i
- Layer 2*
- Layer 3
- Layer four
- Layer 7
twenty. A group of Windows PCs in a new subnet has been added to an Ethernet network. When testing the connectivity, a technician finds that these PCs can access local network resources but not the Net resources. To troubleshoot the problem, the technician wants to initially confirm the IP address and DNS configurations on the PCs, and also verify connectivity to the local router. Which three Windows CLI commands and utilities will provide the necessary information? (Cull three.)
- ping*
- arp -a
- netsh interface ipv6 show neighbor
- nslookup*
- tracert
- ipconfig*
- telnet
21. Users written report that the new web site http://www.company1.biz cannot be accessed. The helpdesk technician checks and verifies that the web site tin can be accessed with http://www.company1.biz:ninety. Which layer in the TCP/IP model is involved in troubleshooting this issue?
- transport*
- application
- network access
- internet
22. Where are IPv4 address to Layer 2 Ethernet address mappings maintained on a host figurer?
- routing table
- ARP cache*
- neighbor table
- MAC address table
23. A networked PC is having trouble accessing the Internet, but can impress to a local printer and ping other computers in the area. Other computers on the aforementioned network are not having any problems. What is the problem?
- The PC has a missing or incorrect default gateway.*
- The link between the switch to which the PC connects and the default gateway router is downwards.
- The switch port to which the PC connects has an incorrect VLAN configured.
- The default gateway router does not have a default route.
24. The newly configured ASBR that connects a company to the Cyberspace has a default route configured and has the default-data originate command entered. Devices connected through this router tin can access the Internet. The problem is that no other OSPF routers have a default route in the routing table and no other users throughout the organization can access the Internet. What could exist the problem?
- The ASBR should utilize the exit_interface argument instead of next-hop on the default route.
- The ASBR does not accept OSPF configured.
- The ASBR does non have an OSPF neighbor.*
- The other routers are not configured to take LSA type 4s.
25. An internal corporate server can be accessed past internal PCs, simply not past external Internet users that should have access. What could be the issue?
- The default gateway router for the server does non have a default route.
- The switch port to which the server connects has an wrong VLAN configured.
- The server does not have a individual IP address assigned.
- Static NAT has not been configured properly or at all.*
26. Make full in the blank.
Employ the enshroud to verify IPv4 address to Layer two Ethernet address mappings on a host computer.
Correct Answer: ARP
27. Open the PT Action. Perform the tasks in the activity instructions and and so answer the question.
A user reports that PC0 cannot visit the web server www.server.com. Troubleshoot the network configuration to identify the problem. What is the cause of the problem?
- The clock charge per unit on Branch S0/0/0 is configured incorrectly.
- A serial interface encapsulation is configured incorrectly.*
- The DNS server address on PC0 is configured incorrectly.
- A default route on HQ is non configured.
Older Version
28. What are the most common syslog messages?
- those that occur when a bundle matches a parameter status in an access command list
- link up and link down letters*
- output messages that are generated from debug output
- error letters about hardware or software malfunctions
29. When logging is used, which severity level indicates that a device is unusable?
- Alert – Level 1
- Critical – Level ii
- Emergency – Level 0*
- Fault – Level 3
30. Refer to the exhibit. Which two conclusions can be drawn from the syslog message that was generated by the router? (Choose two.) 
- This message resulted from an unusual error requiring reconfiguration of the interface.
- This message indicates that the interface should be replaced.
- This message is a level 5 notification message. *
- This message indicates that service timestamps have been configured.*
- This message indicates that the interface changed state five times.
31. A network technician has issued the service timestamps log datetime command in the configuration of the branch router. Which additional command is required to include the date and time in logged events?
- Branch1(config)# service timestamps log uptime
- Branch1# clock set 08:00:00 05 AUG 2013*
- Branch1(config)# service timestamps debug datetime
- Branch1# copy running-config startup-config
32. Refer to the exhibit. From what location have the syslog letters been retrieved? 
- syslog server
- syslog client
- router RAM*
- router NVRAM
33. Refer to the exhibit. What does the number 17:46:26.143 correspond? 
- the time passed since the syslog server has been started
- the time when the syslog bulletin was issued*
- the time passed since the interfaces have been upward
- the fourth dimension on the router when the evidence logging command was issued
34. Which destination do Cisco routers and switches utilise by default when sending syslog messages for all severity levels?
- panel*
- nearest syslog server
- NVRAM
- RAM
35. A network administrator has issued the logging trap 4 global configuration way command. What is the result of this control?
- Later on four events, the syslog client will transport an event message to the syslog server.
- The syslog client will transport to the syslog server any upshot bulletin that has a severity level of 4 and higher.
- The syslog client will ship to the syslog server whatsoever event message that has a severity level of 4 and lower.*
- The syslog client will ship to the syslog server event messages with an identification trap level of only iv.
36. Which statement describes SNMP operation?
- An NMS periodically polls the SNMP agents that are residing on managed devices by using traps to query the devices for data.
- A go request is used past the SNMP agent to query the device for information.
- An SNMP amanuensis that resides on a managed device collects information about the device and stores that information remotely in the MIB that is located on the NMS.
- A set request is used by the NMS to change configuration variables in the agent device.*
37. What are SNMP trap messages?
- messages that are used past the NMS to query the device for data
- unsolicited messages that are sent by the SNMP agent and alert the NMS to a condition on the network*
- messages that are used by the NMS to change configuration variables in the agent device
- letters that are sent periodically by the NMS to the SNMP agents that reside on managed devices to query the device for data
38. Which SNMP feature provides a solution to the chief disadvantage of SNMP polling?
- SNMP set letters
- SNMP trap letters*
- SNMP go messages
- SNMP community strings
39. When SNMPv1 or SNMPv2 is being used, which feature provides secure access to MIB objects?
- bundle encryption
- message integrity
- customs strings*
- source validation
40. A network administrator has issued the snmp-server user admin1 admin v3 encrypted auth md5 abc789 priv des 256 key99 control. What are two features of this control? (Choose 2.)
- It adds a new user to the SNMP group.*
- It restricts SNMP access to divers SNMP managers.
- It forces the network manager to log into the agent to retrieve the SNMP letters.
- Information technology uses the MD5 authentication of the SNMP letters.*
- It allows a network ambassador to configure a hush-hush encrypted password on the SNMP server.
41. How can SNMP access be restricted to a specific SNMP manager?
- Use the snmp-server community control to configure the community string with no access level.
- Specify the IP address of the SNMP director by using the snmp-server host command.
- Use the snmp-server traps command to enable traps on an SNMP director.
- Ascertain an ACL and reference it by using the snmp-server community command.*
42. A network administrator issues two commands on a router:
R1(config)# snmp-server host x.10.fifty.25 version 2c campus
R1(config)# snmp-server enable traps
What can exist concluded afterward the commands are entered?
- No traps are sent, because the notification-types statement was not specified nevertheless.
- Traps are sent with the source IP address as 10.10.l.25.
- If an interface comes up, a trap is sent to the server.*
- The snmp-server enable traps command needs to be used repeatedly if a particular subset of trap types is desired.
43. Refer to the showroom. What can be concluded from the produced output? 
- An ACL was configured to restrict SNMP access to an SNMP manager.*
- This is the output of the testify snmp command without whatever parameters.
- The system contact was not configured with the snmp-server contact control.
- The location of the device was not configured with the snmp-server location command.
44. What is a difference between SNMP and NetFlow?
- Unlike NetFlow, SNMP uses a "push"-based model.
- NetFlow collects more than detailed traffic statistics on IP networks than SNMP does.*
- SNMP only gathers traffic statistics, whereas NetFlow can also collect many other performance indicators, such as interface errors and CPU usage.
- Different NetFlow, SNMP may be used to provide IP accounting for billing purposes.
45. How does NetFlow function on a Cisco router or multilayer switch?
- Netflow captures and analyzes traffic.
- One user connectedness to an application exists as two NetFlow flows.*
- On 2960 switches, Netlow allows for information export.
- NetFlow does not consume any boosted memory.
46. Which type of information can an administrator obtain with the show ip cache flow control?
- the NetFlow version that is enabled
- whether NetFlow is configured on the right interface and in the correct direction
- the configuration of the export parameters
- the protocol that uses the largest book of traffic*
47. Which ii statements describe items to exist considered in configuring NetFlow? (Choose two.)
- Netflow requires both management and agent software.
- Netflow requires UDP port 514 for notification messages.
- NetFlow consumes boosted retention.*
- Netflow can just be used in a unidirectional flow.*
- NetFlow tin can only be used if all devices on the network support it.
48. What is the most common purpose of implementing NetFlow in a networked surroundings?
- to back up accounting and monitoring with consumer applications*
- to actively capture traffic from networked devices
- to monitor live data usage and to control traffic flow with ready letters
- to passively capture changing events that occur in the network and to perform after-the-fact-analysis
49. Refer to the exhibit. While planning an upgrade, a network administrator uses the Cisco NetFlow utility to analyze data flow in the current network. Which protocol used the greatest amount of network fourth dimension? 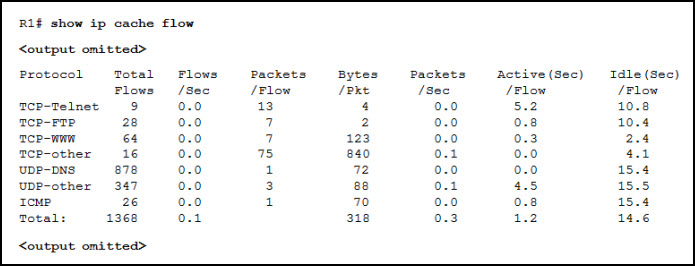
- TCP-Telnet
- TCP-FTP
- TCP-other
- UDP-DNS
- UDP-other *
50. Fill in the bare.
The syslog protocol uses UDP port 514 and is the nearly common method to access organization messages provided by networking devices.
51. When SNMPvl or SNMPv2 is being used, which characteristic provides secure access to MIB objects?
- message integrity
- source validation
- customs strings*
- packet encryption
52. A network administrator has issued the snmp-server user adminl admin v3 encrypted auth md5 abc789 priv des 256 key99 control. What are two features of this command? (Choose two.)
- It forces the network managing director to log into the agent to call back the SNMP messages.
- Information technology restricts SNMP access to divers SNMP managers.
- Information technology uses the MD5 authentication of the SNMP letters.*
- It allows a network ambassador to configure a secret encrypted countersign on the SNMP server.
- It adds a new user to the SNMP group.
53. Which SNMP version uses weak community string-based access control and supports bulk retrieval?
- SNMPv3
- SNMPv1
- SNMPv2c*
- SNMPv2Classic
54. Which protocol or service tin can exist configured to send unsolicited letters to alert the network administrator about a network effect such as an extremely high CPU utilization on a router?
- SNMP*
- NetFlow
- syslog
- NTP
55. Which protocol or service allows network administrators to receive system messages that are provided by network devices?
- SNMP
- syslog*
- NetFlow
- NTP
56. The command ntp server 10.one.ane.ane is issued on a router. What impact does this control take?
- determines which server to send arrangement log files to
- synchronizes the clock of the device to the timeserver that is located at IP address x.1.ane.one*
- identifies the server on which to store fill-in configurations
- ensures that all logging volition have a time stamp associated with it
57. Which syslog message type is attainable only to an administrator and merely via the Cisco CLI?
- alerts
- debugging*
- emergency
- errors
58. Which protocol is used by network administrators to runway and gather statistics on TCP/IP packets that are entering or exiting network devices?
- syslog
- NetFlow*
- NTP
- SNMP
Download PDF File below:
[sociallocker id="54558″]
[/sociallocker]
Source: https://itexamanswers.net/ccna-4-chapter-8-exam-answers-v5-0-3-v6-0-full-100.html
0 Response to "Apush Chapter 28 Review Questions Identification the Baruch Plan"
Post a Comment